This Operational Procedure is issued under the authority of the Commissioner and should be read together with the ACNC Policy Framework, which sets out the scope, context and definitions common to our policies.
Context statement
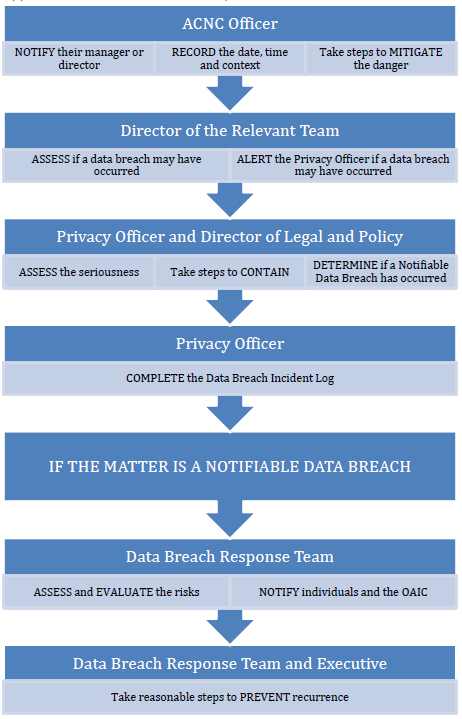
- This Data Breach Response Plan (Response Plan) sets out the procedure to be followed by ACNC staff if the ACNC experiences a data breach, or suspects that a data breach has occurred. The flowchart at Appendix A of this document sets out this procedure.
- A data breach occurs when the following happens:
- personal information is lost or accessed, modified, misused, or disclosed without authorisation. Personal information means information that identifies or could reasonably identify an individual, whether or not it is true or recorded (section 6 of the Privacy Act 1988 (Cth) (‘Privacy Act’)).
- protected ACNC information is used or disclosed in a way that is not permitted under the secrecy provisions in the ACNC Act. Protected ACNC information is defined in section 150-15 of the Australian Charities and Not-for-profits Commission Act 2012 (Cth) (‘ACNC Act’) as information disclosed or obtained under or for the purposes of the ACNC Act that relates to the affairs of an entity and identifies, or can be used to identify, the entity.
- confidential information is lost or accessed, modified, misused, or disclosed without authorisation. Confidential information is information to which confidentiality obligations are attached – for example, information that the ACNC has received from a third party that is subject to a confidentiality agreement, Memorandum of Understanding, or a contractual arrangement.
- A piece of information can be any combination of personal information, protected ACNC information, and confidential information at the same time.
- Data breaches may be caused by technological problems, human error, deliberate action by an ACNC officer, or a malicious action by a third party (such as an IT system hack).
- When a breach involves protected ACNC information both the Response Plan and the ACNC Act must be considered.
- The Notifiable Data Breaches Scheme (NDBS) may also impose additional responsibilities where the breach of personal information is likely to result in serious harm to any individual (including people who are not the subject of the personal information). The NDBS is discussed in greater detail below.
- The Office of the Australian Information Commissioner (OAIC) is only concerned with breaches that involve personal information. Data breaches that involve protected ACNC information that is not personal information do not need to be reported to the OAIC.
- All ACNC staff, the ACNC Commissioner, Advisory Board members and external service providers have responsibilities under this procedure.
- The Privacy Officer is the primary point of contact for privacy matters and has certain responsibilities in relation to data breaches, some of which are detailed in this procedure.
What to do when a suspected data breach is identified
Notify director and manager, and the Privacy Officer
- Once an individual is aware of a suspected data breach, they must immediately notify their director and manager if they are ACNC Staff, or the Privacy Officer if they are the Commissioner, a member of the Advisory Board or an external service provider.
- The individual should record the time and date that the suspected breach was discovered, the type of information involved, the cause and extent of the breach, and the context of the information and the breach. This information all becomes part of the Privacy Officer’s assessment of the breach.
- Where steps can be taken to contain the suspected data breach, the individual should do so as soon as possible. Examples include trying to recall an email sent to an incorrect recipient; asking the recipient to delete the email; or taking steps to withhold or remove a document that was incorrectly published on the ACNC Charity Register. Remember not to wholly delete documents or records related to the breach, as this may impede the Privacy Officer’s later assessment (although any person outside the ACNC that incorrectly received the information should be requested to permanently delete the information).
- The individual of the relevant team will assess and determine whether a data breach may have occurred, and consult with their manager (and director as necessary). If unsure whether to consult with your director, speak to your manager. If the individual, their manager or director reasonably suspects that a breach has occurred, they must immediately complete and send a data breach notification form (available on the Legal and Policy SharePoint homepage) by email to privacy@acnc.gov.au which is accessed by the Privacy Officers and Director of Legal & Policy, and copy their manager and director.
Privacy Officer and Director Legal and Policy to assess the seriousness of the breach
- Once a data breach has been reported, the Privacy Officer should take any reasonable steps to contain the breach that have not already been taken. Containment should only be delayed in the highly unlikely event that the steps to contain the breach may have their own consequences that outweigh the privacy risk. In such cases, the Privacy Officer should discuss available options with the Director Legal and Policy.
- For more serious cases (see Notifiable Data Breaches), decisions about containment may be referred to the ACNC Data Breach Response Team.
- The Privacy Officer and the Director Legal and Policy must assess the nature, scope, and seriousness of the breach. A data breach is more likely to be serious where one or more of the following factors apply:
- many people or entities experience an impact,
- the nature of the information poses an increased risk to those affected,
- where there is a real risk the breach may result in serious harm to an individual,
- the breach may indicate a systemic problem that could have a wide-ranging impact, or
- the breach was done purposefully.
- A minor breach has been sufficiently dealt with when the Director of Legal and Policy is comfortably satisfied that there is no real risk of further serious harm to an individual and all reasonable steps have been taken to:
- mitigate the risk of harm to an individual,
- remedy any reputational damage, such as by apologising to the affected parties, and
- reduce the risk of repeat occurrences. The Privacy Officer and the Director Legal and Policy may provide guidance to the ACNC staff member and/or their director to ensure similar data breaches do not occur in the future.
- The Privacy Officer will record relevant details in the Data Breach Incident Log and the Data Breach Response form. The following details must be recorded:
- description of the breach or suspected breach,
- action taken by the director or ACNC staff member to address and contain the breach or suspected breach,
- outcome of that action,
- an assessment of the risk that the breach may result in serious harm to any person,
- confirmation from the Director of Legal and Policy that no further action is required, and
- confirmation that the incident has been recorded in the ACNC Data Breach Incident Log.
- The record of the breach must be saved in the SharePoint Folder. If the breach is serious, it must immediately be escalated to the Data Breach Response Team.
Notifiable data breaches
- The Privacy Act requires the ACNC to notify individuals and the OAIC about data breaches that are likely to cause serious harm. These types of breaches are referred to as ‘notifiable data breaches’. The requirements of the NDBS are contained in Part IIIC of the Privacy Act.
- A data breach is notifiable if it is likely to result in serious harm to any individuals. Whether the data breach is likely to result in serious harm requires an objective assessment on a case-by-case basis. For example, unlawfully disclosing a person’s address will often be a notifiable breach – it may not be an especially sensitive detail for most people, but, unless there is evidence to the contrary, objectively speaking it is entirely plausible that the person keeps their address secret because of a genuine safety concern.
- The OAIC publishes a six-monthly report, which shows that relatively simple errors can carry enough risk to be considered a notifiable data breach, such as using the ‘CC’ function rather than the ‘BCC’ function when sending an email.
- The OAIC has outlined that a notifiable data breach arises when three criteria are satisfied:
- there is unauthorised access to or disclosure of personal information, or a loss of personal information,
- that is likely to result in serious harm to one or more individuals, and
- the entity has not been able to prevent the likely risk of serious harm with remedial actions.
- The Privacy Officer will assess whether a data breach involving personal information is a notifiable data breach and this assessment will be reviewed by the Director Legal and Policy.
- If it is determined that a data breach is a notifiable data breach, it must be escalated to the Data Breach Response Team. The Privacy Officer will ensure the requirements of the NDBS are met.
Data Breach Response Team
Composition
- The Response Team must include:
- The Privacy Officer,
- The Director of Legal and Policy,
- The Director of IT, and
- The Director of the team that was responsible for the breach.
- Responding properly to a notifiable data breach is considered priority work, and the above members of the Response Team are expected to be involved. They should designate a proxy only in exceptional circumstances.
- The Response Team may include, on a case-by-case basis, the Privacy Champion, and another other ACNC officer who, because of their expertise or the nature and functions of their role, may be required to help identify and mitigate the risks as effectively as possible.
Process
- The Response Team must work in consultation with the Executive in responding to the breach. It will undertake an assessment of the risks involved and using that risk assessment as the basis for deciding what actions to take in the circumstances.
- There are four key steps to consider when responding to a breach or suspected breach. Generally, steps 1-3 should be carried out concurrently or in close succession.
- Step 1: Contain the breach and do a preliminary assessment
- Step 2: Evaluate the risks associated with the breach
- Step 3: Notification
- Step 4: Prevent future breaches
Step 1: Contain the breach and do a preliminary assessment
- Once a data breach has been identified, action must be taken to immediately contain it. For example: stop the unauthorised practice; recover the records; or shut down the system that was breached. The Response Team may direct any ACNC staff to take all necessary and lawful steps to contain the breach.
- Move quickly to appoint someone to lead the initial investigation. In some instances, this may be a member of the Response Team. In other instances, it will be a person most suitably qualified to carry out the initial investigation (as determined by the members of the Response Team).
- In some situations, it will be necessary to assemble a team that includes representatives from appropriate areas of the ACNC to conduct the preliminary assessment. The following questions should be answered during the preliminary assessment:
- What information does the breach involve?
- What was the cause of the breach?
- What is the extent of the breach?
- What are the harms (to affected persons) that could potentially be caused by the breach?
- How can the breach be contained?
Step 2: Evaluate the risks associated with the breach
- A thorough evaluation of the risks will assist the ACNC in determining the appropriate course of action to take. The following factors are relevant when assessing the risk:
| The type of information involved |
|
| The context of the information and the context of the breach |
|
| The cause and extent of the breach |
|
| The risk of harm to the affected persons |
|
| The risk of other harms |
|
Step 3: Notification
- Typically, if a data breach creates a real risk of serious harm to a person, the affected person should be notified. Only the affected person knows the true extent of the risk and can usually take more effective steps to offset the risk than the ACNC can. Consider whether notification would significantly empower someone impacted by a data breach to reduce any risk of harm to them. If the answer is yes, notification is likely to be a necessary step. Consider the following factors:
- What is the risk of serious harm to the person, as determined by step 2?
- Is the person able to avoid or mitigate possible harm if notified of a breach (in addition to steps taken by the agency or organisation)?
- Even if the person would not be able to take steps to fix the situation, is the information sensitive or likely to cause embarrassment?
- What are the legal and contractual obligations to notify and what are the consequences of notifying and not notifying?
- Notification should occur as soon as possible. However, in some instances, delay may be necessary. This process will ordinarily be carried out by the Privacy Officer, under the oversight of the Director Legal and Policy. The customer service aspect may also be relevant to deciding who should be responsible for notifying the person involved – sometimes it may be appropriate for a senior staff member, Assistant Commissioner or Commissioner to use the opportunity to extend an apology and demonstrate that we are taking the breach seriously.
- Notification should be direct – by phone, letter, email, or in person, to the affected individuals. Indirect notification, either by website, posted notices or media should only occur where direct notification could cause further harm, is cost prohibitive or the contact information for affected persons is unknown.
Details to include in the notification
- The content of the notification will vary depending on the breach and method of notification. However, notification should generally include:
- a description of the incident,
- detail of the type of information involved,
- response to the breach,
- an offer of assistance to affected persons, and
- the ACNC’s contact details.
- In addition, it may be appropriate to include:
- other information sources designed to assist in protecting against identity theft or interferences with privacy (e.g., www.oaic.gov.au),
- whether the OAIC or anyone else has been notified of the breach,
- legal implications (e.g., the secrecy provisions), or
- how individuals can lodge a complaint with the ACNC and/or the OAIC.
Notifying third parties
- Third parties may be notified when it is appropriate and when there is a lawful and valid reason to do so. In responding to a data breach, staff should not compound the problem by unnecessarily sharing the information even further. The ACNC must notify the OAIC of all notifiable data breaches, but we may choose to notify other parties such as:
- police,
- insurance providers,
- credit card companies, financial institutions,
- professional or other regulatory bodies, and/or
- agencies that have a direct relationship to the information.
Step 4: Prevent further breaches
- Once immediate steps have been taken to mitigate the risks associated with a breach, the ACNC must take the time to investigate the cause of the breach. The ACNC Executive must be briefed on the outcome of the investigation, including any recommendations to change to policies and procedures, revise staff training, or develop new staff training.
References
| Version | Date of effect | Brief summary of change |
| Version 1 - Initial operational procedure | 03/02/2015 | Initial operational procedure endorsed by the Commissioner on 03/02/2015 |
| Version 2 - Revised operational procedure | 14/09/2021 |
Updated and revised response process to reflect current actions more accurately. Included section on Notifiable Data Breaches Scheme. Reconfigured Data Breach Response Team. Moved to new template. |